Introducing Keepabl's PRIVACY STACK
A structure to help understand what's needed for Privacy compliance
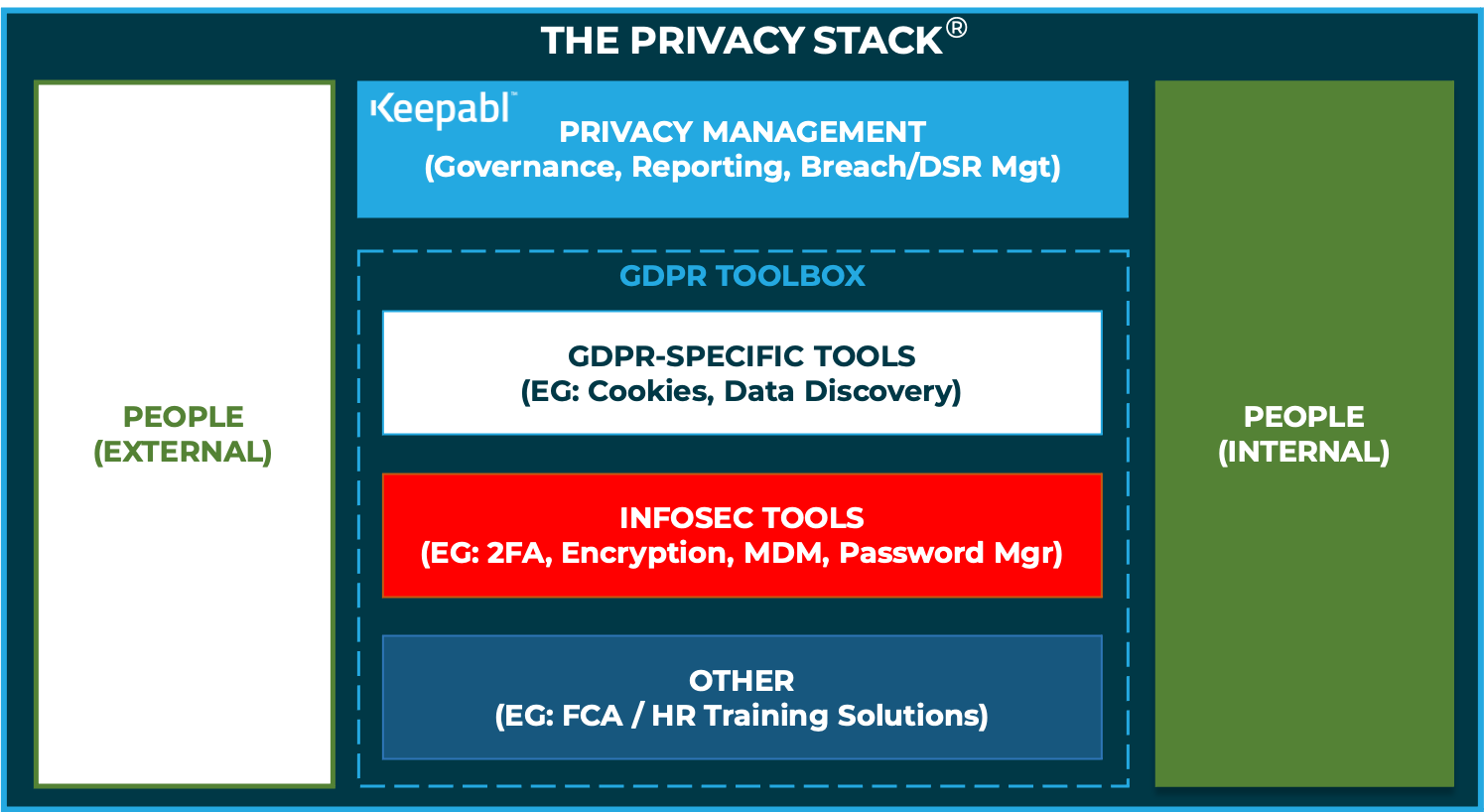
The Privacy Stack
Here at Keepabl, we often say that the Privacy sector, kickstarted into life by GDPR in 2018, is 30 years behind Security as a practice and industry. Compared to Security, with well-established roles and remits within an organisation and well-established categories of vendors and advisors, organisations are still trying to determine what help and resources they need to build out and maintain their Privacy compliance.
That’s why we at Keepabl created the Privacy Stack! It’s a really helpful methodology for organisations to identify the services and solutions they need to consider for their Privacy compliance. And it’s a great way for us to identify leading solutions that address compliance in a simple, user-focused way.
We’ve found it extremely useful in talking to clients about what they need for GDPR compliance – it really seems to resonate. We hope you find it helpful.
The Need
While each organisation may claim to be unique, all have common problems in addressing their GDPR and broader Privacy obligations – and many are struggling to work out just exactly how to handle that compliance.
Compare it to Security – you know you have to have 2FA, password managers, encryption, a firewall, VPNs etc – all chosen to address your risk profile and most likely not all from one provider. You’ll have a person who rolls up their sleeves to understand and manage your holistic approach to Security, usually with the help of skilled advisors and practitioners.
Now look again at Privacy… still expecting to have a single kettle, that’s a toaster … and a fridge … and an oven…?
Why ‘Stack’?
Just as Keepabl’s Privacy SaaS solution makes getting and staying compliant with GDPR much simpler, the Privacy Stack clarifies the thought process around what you need to have or do to address your GDPR and broader Privacy obligations.
We’re all familiar with the concept of a Tech Stack: a collection of infrastructure, networks, servers, databases, applications and other technology that you use to deliver a desired outcome, chosen so that they all play well together.
The Privacy Stack is exactly that for Privacy compliance, with the addition of essential humanware!

Going forward, we’ll be identifying the sort of services and solutions you need in your Privacy Stack, identifying advisors you should have on speed-dial as well as great solutions to consider. We’ll also recognise you’ve already got plenty you can repurpose or co-opt, for example from your Information Security tech stack, FCA solutions, or other compliance providers. For now, let’s take a quick look at the component parts of the Privacy Stack.
Humanware
It all starts with your own people. Someone at the organisation (preferably more than one) has to roll their sleeves up and become the Privacy Champion. They then need to get support for and manage the initial ‘get compliant’ project, enthusing and involving the rest of the business.
You’ll likely use external advisers at this stage, such as your law firm, your managed service provider (MSP) or compliance or privacy consultants. In this ‘get compliant’ phase, they’ll help you inventorise your personal data (hopefully using a solution like Keepabl to capture that investment of time and effort and create instant gap analysis and reports). They’ll also help review and update policies and procedures, carry out DPIAs and help put in place your Privacy Governance System (perhaps using Keepabl’s Privacy Policy Pack).
You’ll then move into the ‘business as usual’ or ongoing compliance phase. Your advisers are likely to stay involved on an ongoing basis to varying degrees depending on your internal resources, perhaps helping if you suffer a suspected breach, or with reviewing vendors or contracts, assisting if there’s an audit, and providing training. You can use Keepabl to review the entirety of your governance system with them over a period, much as you maintain your Information Security Management System if you’re ISO 27001 certified.
Software
After people, it’s the software you use to meet most of the technical requirements of compliance and make the humans’ job as easy as possible. It’s important to note that no one piece of software will cover all your privacy needs, just as you use different providers for backups or anti-virus, data discovery or encryption. So you’ll need to identify the jobs to be done and choose relevant tools accordingly. That’s where the Privacy Stack comes into its own and lights the way.
While GDPR isn’t a technology law, nor a pure security law, technology and security are fundamental to GDPR compliance. Tools such as 2 or multi-factor authentication (‘2FA’ and ‘MFA’), encryption, backup services, secure transfer services, and other security software such as firewalls and anti-virus software, either should or could have a place in your Privacy Stack. Some will be solely utilised for GDPR compliance, but you should be able to leverage your existing investments in tools for other compliance requirements and, importantly, your existing information security tools.
Hardware
Hardware is less critical for the Privacy Stack as we’re not talking about the hardware you use in the normal course of your working day, such as laptops, smartphones and even the servers and other media where the data is stored. (You will need to consider that hardware as part of your Privacy Governance though, including to encrypt data at rest.) Here, we’re talking about hardware that you use specifically for GDPR compliance, such as encryption hardware and the kit you might need for your chosen MFA solution.
That’s a quick walk through the Privacy Stack. We’ll be discussing all of these elements of the Privacy Stack in later blog posts so do keep tuned!
Related Articles

Blog
DSRs or Individuals' Rights: A Backgrounder
Data Subject Rights or DSRs have been around for decades, but GDPR massively reinforced and extended them when it took effect in 2018 – five years ago now. Laws around the […]

Blog
The 2022 Year in Privacy Hurdles
It’s back! The Year in Privacy Hurdles burst onto the scene at the end of 2021, bringing together the big action in Data Protection in the UK and EEA […]

